A couple of months ago, I moved my blog from wordpress.com to my own hosting on Azure. Afterwards, I setup SSL using a Let’s Encrypt free certificate. This process is using an opensource plugin into App Service to communicate to Let’s Encrypt.
Recently, Microsoft announced free certificates for App Service custom domains. These certs are free of charge, and rotated automatically by Microsoft. Although the extension that managed my Let’s Encrypt certs rotates them using a webjob, I thought why don’t I switch to free managed certs and let Microsoft take care of everything.
In this post I’ll walk you through the setup of these free certs. I hit an issue during the setup of this and I’ll explain the solution for this after walking you through the end-to-end experience.
Let’s have a look.
Setting up App Service certificates
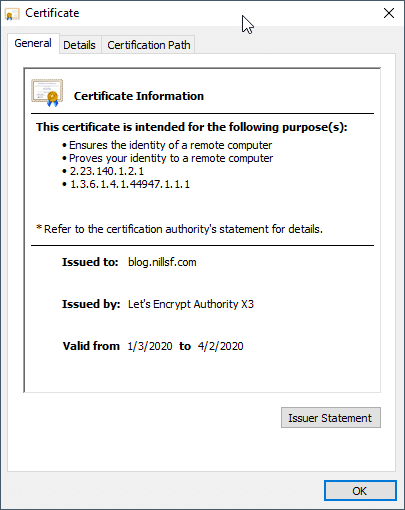
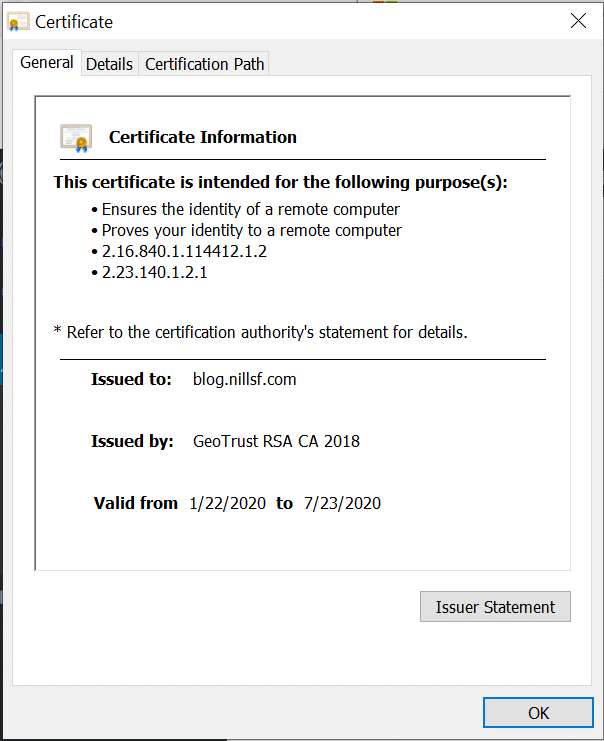
Let’s start by having a look at my current cert:
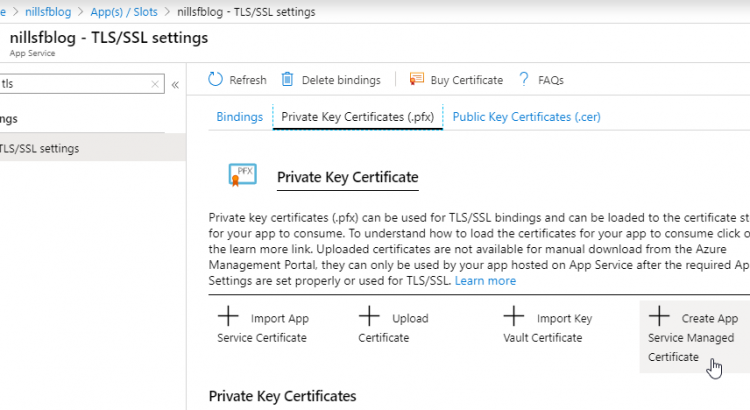
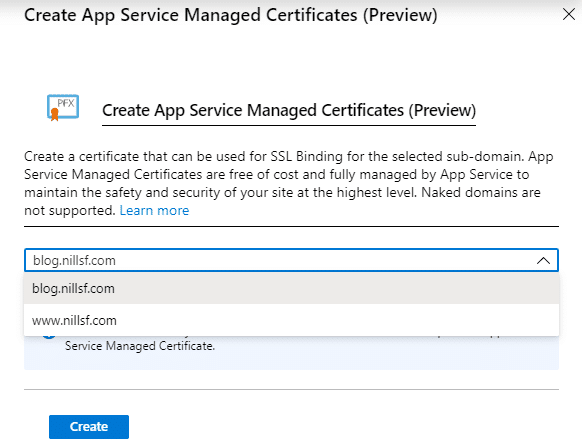
Let’s go over to the Azure portal, and open our Web App. In that view, you can look for ‘TLS’ in the left hand navigation, and then hit Private Key Certificates on the top. Here you will find the option to Create a new Certificate.
These free certs don’t support wildcards, so each subdomain will require its own certificate. I’ll get one for both my subdomains (www and blog. www does a redirect to blog for now).
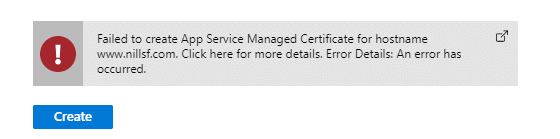
And this is where I hit an error. I’ll walk through the solution in the end.
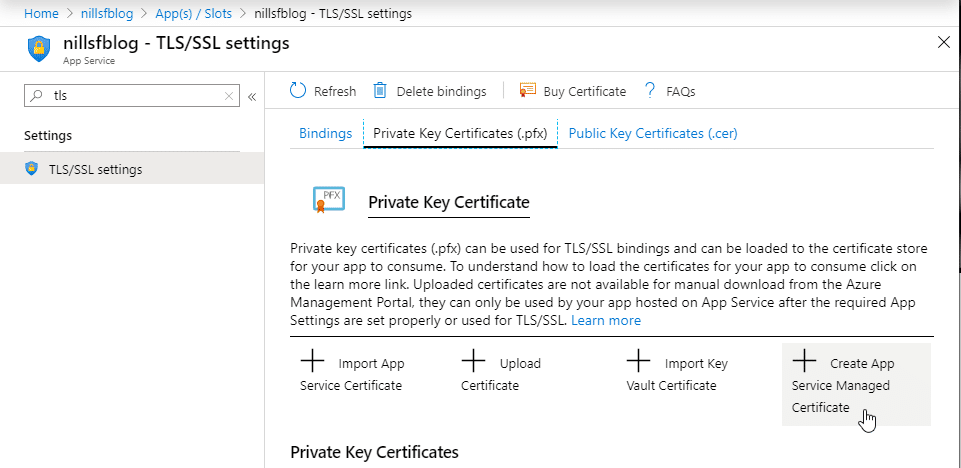
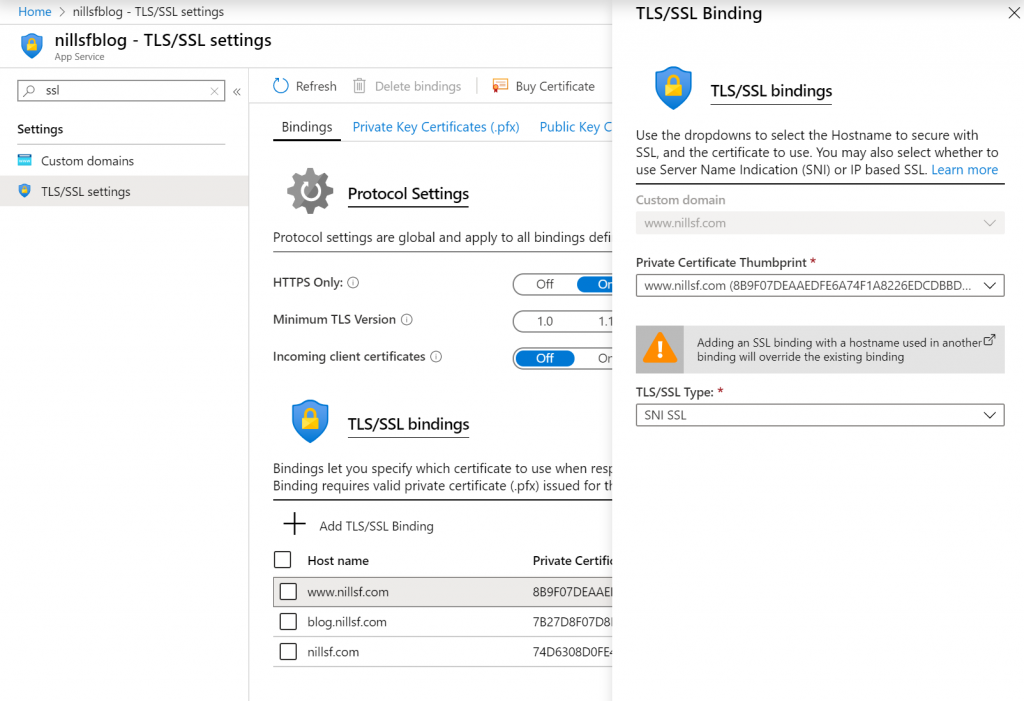
Once the cert was created, there just remains the changing of the binding.
To change the binding, note down the certificate fingerprint from the new certificate. Head over to the bindings page (top hand navigation) and select the domain where you want to change the binding.
And from here on forward, we should be using the new cert. Which I verified in the certificate information in my browser.
Solving the error
As I mentioned before, I hit an error in creating the managed certs.
@AzureSupport Looks like I’m unable to create an App Service certificate. It fails for both https://t.co/vfM5ZeWYzm and https://t.co/7esYUoVLMr (www redirects to blog). Currently using Let’s Encrypt, and was hoping to switch. pic.twitter.com/VIIDxH6izP
— Nills Franssens (@NillsF) January 23, 2020
I was helped through Azure support on Twitter and opened a support case in the end. The issue seemed to be that I was using A records in stead of CNAME records for DNS. So I headed over to my DNS system (namecheap.com) and changed my A to CNAME records. I gave that a couple minutes and that solved this issue. As a good guy, I also created a PR against the Azure documentation to point this out.
Conclusion
It was rather easy to switch from the Let’s Encrypt extension to free certificates, except for the DNS issue I ran into. This makes it a bit easier to manage my certs, and removes the dependency from Let’s Encrypt.